FortiClient (Malaysia)

Image via fortinet.com
Protect your endpoints and manage everything with ease to stop cyber threats in their tracks.
- Secure your endpoints effortlessly with advanced threat detection and rapid response.
- Manage all your devices and policies from one easy-to-use platform.
- Get complete visibility into your devices to identify vulnerabilities and stay compliant.
What is a FortiClient?
FortiClient is an all-in-one security solution offering antivirus, secure Virtual Private Network (VPN), web filtering, and firewall to protect your devices. It integrates with Fortinet’s Security Fabric for centralized management, ensuring protection against cyber threats while maintaining productivity.
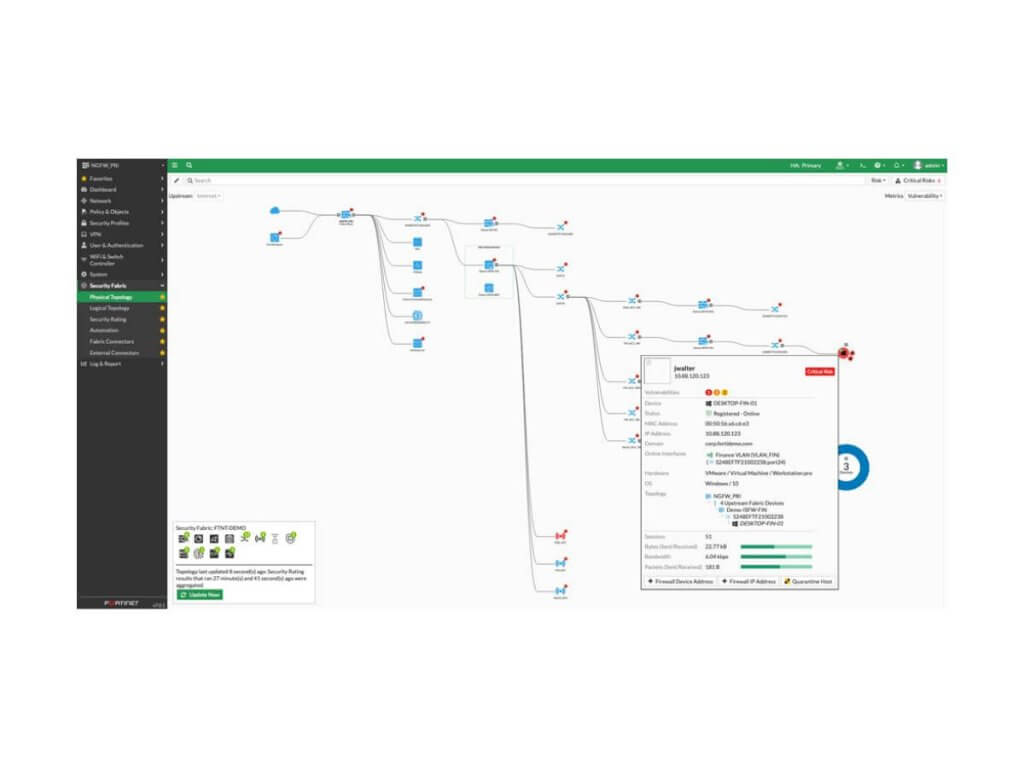
Image via fortinet.com
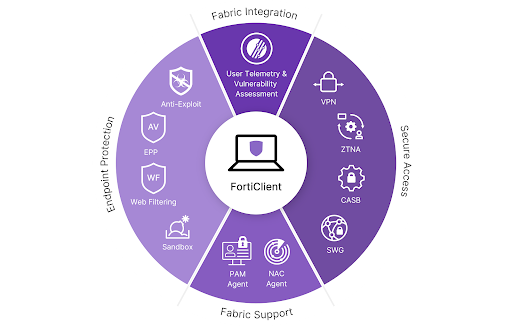
Image via fortinet.com
Features and Capabilities
Deploy this lightweight client on your devices to deliver complete cybersecurity protection.
Broad Endpoint Visibility
Monitor and analyze your network in real-time with FortiClient’s broadband visibility, giving you instant insights into bandwidth, applications, and protocols. Optimize performance, boost security, and stay compliant effortlessly.
Compliance Control
Automate compliance monitoring, create and enforce policies, receive real-time alerts, track changes with an audit trail, and manage everything easily from a single console. Stay ahead of regulations like HIPAA, PCI-DSS, and GDPR effortlessly.
Vulnerability Management
Secure your organization’s infrastructure with FortiClient Fabric Agent. Detect and fix vulnerabilities before they’re exploited using powerful endpoint scanning, automated patch management, prioritized risk assessment, compliance monitoring, and centralized security management.
Automated Response
Detect, contain, and remediate threats in real time with FortiClient Fabric Agent. Centralized management and enhanced visibility simplify endpoint security, reduce risks, and keep your network protected.
Models and Specifications
Safeguard desktops, laptops, and mobile devices with advanced protection tailored to your needs.
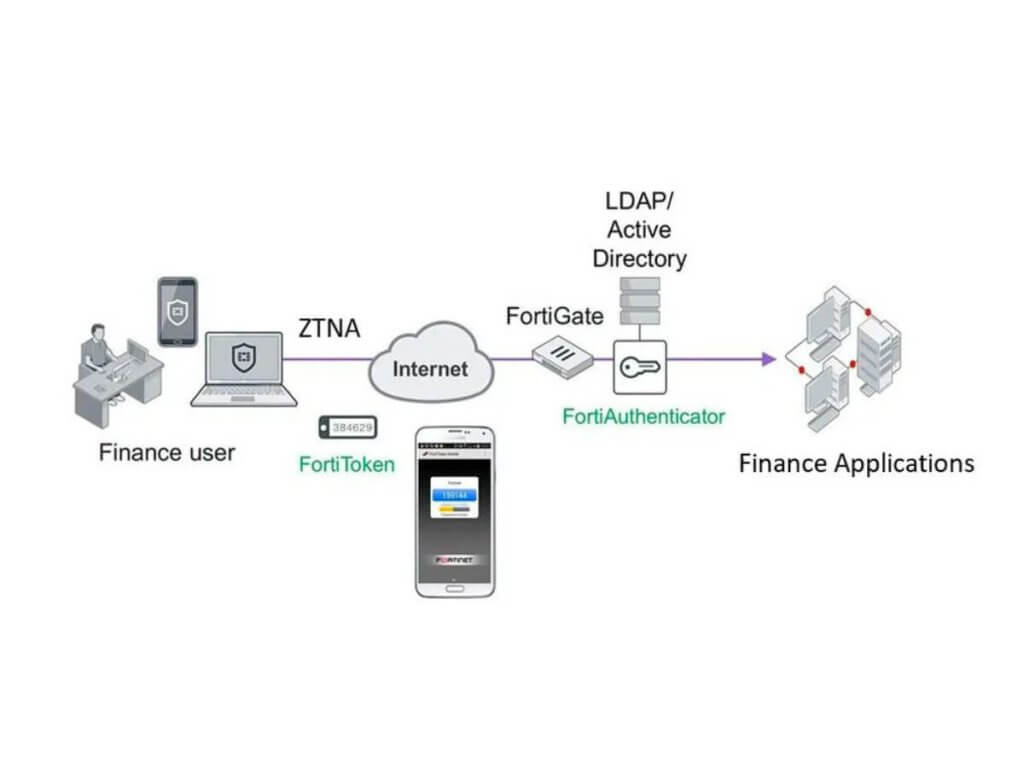
Image via fortinet.com
FortiClient is an endpoint security and protection solution developed by Fortinet. In addition to traditional antivirus capabilities, FortiClient includes several other security features that work together to provide comprehensive protection.
Secure your internal applications with FortiClient’s ZTNA Edition. Grant VPN-free access based on least privilege, protect with TLS encryption and two-factor authentication, and block threats with user behavior analytics and endpoint detection.
Protect your business from advanced cyber threats with FortiClient’s EPP/APT Edition. Detect malware with machine learning, block attacks using sandboxing and behavioral analysis, and secure endpoints with web filtering and application control.
Manage all your endpoint devices seamlessly with FortiClient EMS. Monitor health, push updates, enforce policies, and tackle security threats in real time. Ensure compliance, stay protected with the latest updates, and scale effortlessly to manage thousands of endpoints.
Secure your sensitive data using powerful SSL and IPSec protocols, gain full visibility and control over your network, and monitor, detect, and report incidents with ease. Scalable for any business size, FortiClient ensures efficient and secure VPN connections.
Get the Best Price for FortiClient
Securely connect your devices and stay ahead of cyber risks with the ultimate endpoint security.
Unmatched Third-Party Certifications and Recognitions





These certifications and recognitions highlight the effectiveness and reliability of FortiClient as a comprehensive security solution, providing organizations with the confidence they need to secure their endpoints and data against a wide range of cybersecurity threats.
FAQs on FortiClient
A complete endpoint security solution called FortiClient guards endpoint devices, including laptops, desktop computers, and mobile phones, from various online dangers like malware, viruses, phishing scams, and other cyberattacks.
To secure the endpoint security of devices, it offers a range of security capabilities, including antivirus and anti-malware protection, web security (helps block malicious sites), firewalls, VPNs, and vulnerability assessments.
Corporations and organizations frequently use FortiClient to secure their networks and safeguard critical data.
FortiClient is a VPN client that works by establishing a secure tunnel between the client device and a Fortinet VPN gateway.
- Authentication: The user initiates the connection request by providing their login credentials, such as username and password.
- Encryption: FortiClient uses encryption to protect the data being transmitted between the client device and the VPN gateway. This ensures that the data is not intercepted or tampered with during transit.
- Tunnel Creation: FortiClient creates a secure tunnel between the client device and the VPN gateway. This tunnel is used to transmit data between the two endpoints.
- Data Transfer: Once the tunnel is established, the client device can securely access resources on the VPN network, such as files, applications, and other resources.
- Termination: When the user disconnects from the VPN, the secure tunnel is terminated, and the connection is closed.
Fortinet is one of the top network security solutions providers in the industry. With its award-winning Security Fabric platform, it provides comprehensive protection for organizations’ networks and endpoints from ever-evolving threats.
The key advantage that sets Fortinet apart from other security vendors is its Security Fabric architecture.
This comprehensive security platform with central management administer protection across all network layers, from the endpoint to the cloud, making it easier for organizations to detect and eliminate threats quickly and efficiently.
Other Products From Fortinet
Discover how products within Fortinet Security Fabric protect your assets against security breaches.
Get top-rated network security protection from threats with this scalable next-generation firewall solution.
Protect your web applications from common vulnerabilities with this application security appliance.
Upgrade your network with adaptable access points, offering secure wireless connectivity for any setting.
Get Advanced Endpoint Protection with FortiClient
Make sure your business in Malaysia is safe with the ultimate endpoint security and protection solution: FortiClient. Act now and keep malicious threats away from your Malaysian operations.
Get ahead of the game – get FortiClient today to experience maximum safety for your devices.