Cybercriminals have proven to be very clever and resourceful, often more innovative than the organizations trying to stop them.
Cybercriminals have been particularly successful at compromising systems by targeting applications. Applications can provide an attacker a way into an organization’s network and data, which is why application security is so important.
Fortunately, there are steps organizations can take to help protect their applications from attack. This blog post will discuss how organizations can safeguard their applications and what best practices should be followed.
What is Application Security and Why Does It Matter
Application security (AppSec) refers to the practices and tools that protect software from unauthorized access and exploitation. As cybersecurity threats grow more sophisticated, attackers increasingly target the application layer, the most exposed part of a system.
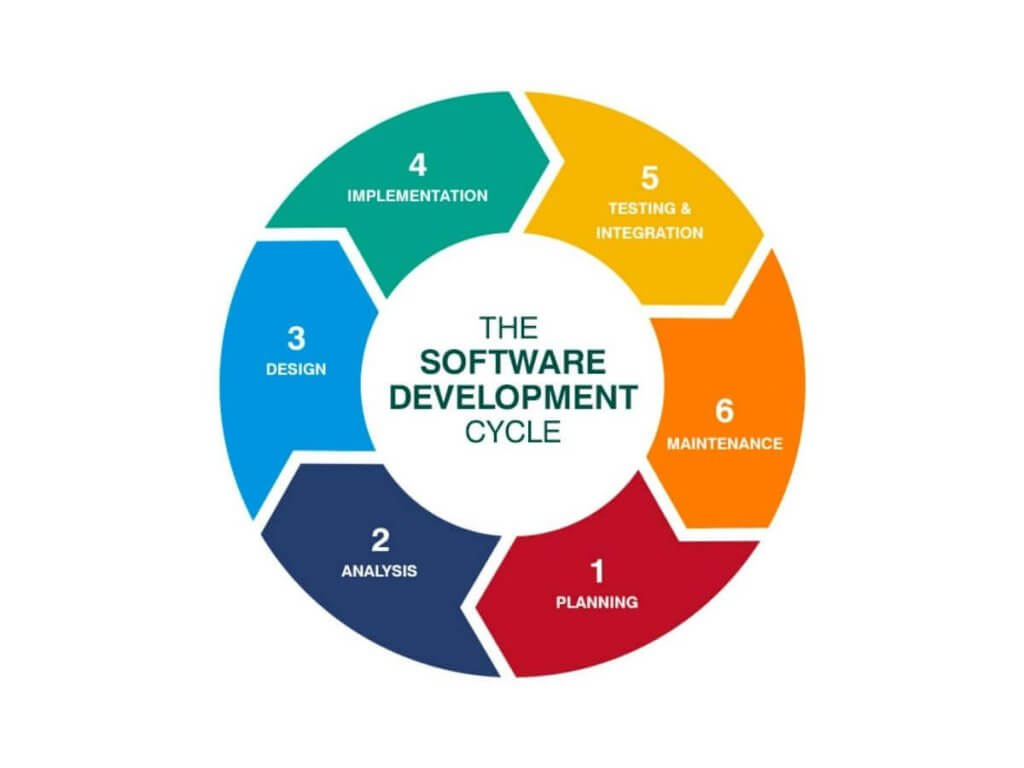
Effective application security requires embedding security throughout the software lifecycle from design and development to testing, deployment, and maintenance. This includes:
- Secure coding practices
- Encryption & data protection
- Vulnerability assessments & penetration testing
- Proper access control mechanisms
With modern applications relying on third-party libraries, legacy systems, and cloud services, security must be continuous and adaptive to protect against evolving threats.
Web Application Security
Web application security protects web servers, applications, and APIs from internet-based threats. Its goal is to defend sensitive data, users, and organizations against risks like data breaches, service disruption, and financial loss. As web applications handle everything from online shopping to financial transactions, they have become a key part of modern business operations and a top target for cyberattacks.
Organizations must understand the common vulnerabilities that threaten web applications and APIs to stay secure. Recognizing these risks is the first step toward building resilient systems that withstand evolving threats.
Understanding Web Application Security Vulnerabilities
The Open Web Application Security Project (OWASP) identifies and categorizes the most critical risks in its widely recognized OWASP Top 10 list. This list highlights the most common and impactful security issues that developers and security teams should prioritize to protect applications from cyberattacks.
- Broken Access Control: Occurs when users perform actions beyond their authorized privileges, such as accessing other users’ data or escalating permissions. This typically arises from missing or weak authorization controls and is one of the most critical and frequently exploited flaws.
- Cryptographic Failures: Poor encryption implementation or failure to protect sensitive data, including passwords, personal information, and financial records, can lead to data leaks. Common problems include storing data in plain text, using outdated algorithms, or improper cryptographic key management.
- Injection: This category includes SQL, NoSQL, OS command, and LDAP injection attacks, where malicious inputs cause unintended commands to execute on the server. These attacks can lead to unauthorized data access, corruption, or full system compromise.
- Insecure Design: Security weaknesses resulting from design flaws, such as missing threat modeling, insecure architecture, or absent security controls during development, increase the attack surface.
- Security Misconfiguration: Default settings, unnecessarily enabled services, or exposed administrative interfaces can expose data, allow unauthorized access, or execute remote code. Proper configuration management is essential.
- Vulnerable and Outdated Components: Use of third-party libraries, frameworks, or software with known vulnerabilities exposes applications to attacks. Regular updating and patching of dependencies are critical.
- Authentication Failures: Weak authentication mechanisms, like poor password policies or broken session management, allow attackers to compromise accounts or impersonate users.
- Software and Data Integrity Failures: Failure to maintain software and data integrity, including supply chain attacks, tampering, or unauthorized modifications, can compromise applications and systems.
- Security Logging and Monitoring Failures: Insufficient logging and alerting delay attack detection and response, enabling breaches to go unnoticed and cause more damage.
- Server-Side Request Forgery (SSRF): Attackers exploit SSRF vulnerabilities by tricking servers into making unintended requests, exposing internal systems or sensitive data not directly accessible externally.
Major API Security Vulnerabilities
APIs are essential for modern applications, but also introduce a wide range of attack surfaces. Below are some of the most critical API-specific risks developers and security teams should address:
- Broken Object Level Authorization (BOLA): APIs often expose endpoints handling object IDs. Attackers can manipulate these IDs to access unauthorized data when proper authorization checks are missing. This is also known as Insecure Direct Object References (IDOR).
- Broken Authentication: Weak or poorly implemented authentication allows attackers to steal credentials or tokens, impersonate users, or bypass authentication mechanisms entirely.
- Broken Object Property Level Authorization: Even when access to an object is authorized, APIs may expose or allow changes to sensitive properties (e.g., user roles or permissions) that should be restricted, leading to data leakage or manipulation.
- Unrestricted Resource Consumption: APIs that do not limit requests or resource usage can be exploited to launch denial-of-service (DoS) attacks or inflate infrastructure costs.
- Broken Function Level Authorization: Complex APIs often expose multiple functions with different access levels. Without strict authorization controls, attackers may access privileged operations only for admins or internal use.
- Unrestricted Access to Sensitive Business Flows: APIs that allow actions like placing orders or submitting comments without rate limiting or abuse detection can be targeted for automated attacks, such as fraud or spam.
- Server-Side Request Forgery (SSRF): When APIs fetch remote resources using user-supplied URLs, attackers may trick the system into accessing internal-only services or sensitive endpoints, bypassing network controls.
- Security Misconfiguration: APIs with unnecessary HTTP methods, verbose error messages, default credentials, or overly permissive CORS settings expose the application to excessive risk.
- Improper Inventory Management: Exposed legacy, staging, or undocumented APIs are often overlooked during security reviews and can be exploited due to weaker controls or outdated dependencies.
- Unsafe Consumption of Third-Party APIs: Trusting external APIs without validating responses or sanitizing data can expose the system to injection attacks or supply chain vulnerabilities.
Application Security Solutions: Protect Your Business from Cyber Threats

Application security is essential to defend your systems from evolving cyberattacks. Spectrum Edge offers effective solutions like Web Application Firewalls (WAF), API security tools, and real-time protection to safeguard your applications. Whether you need secure development practices or runtime defenses, our team can help you build a strong security posture. Contact us today to protect your applications and keep your business safe.